Best Practices to Transition Back to Work
May 27, 2020
After months of time spent discussing how to make the transition to remote work, where and when to implement new tools, and strategies to stay connected and focused on the tasks at hand, many organizations are now looking at the next step that must be made: a return to work. There are a lot of questions but thankfully, there is a wide array of tools to ensure safety and security upon workforce re-entry.
Touchless Access Control
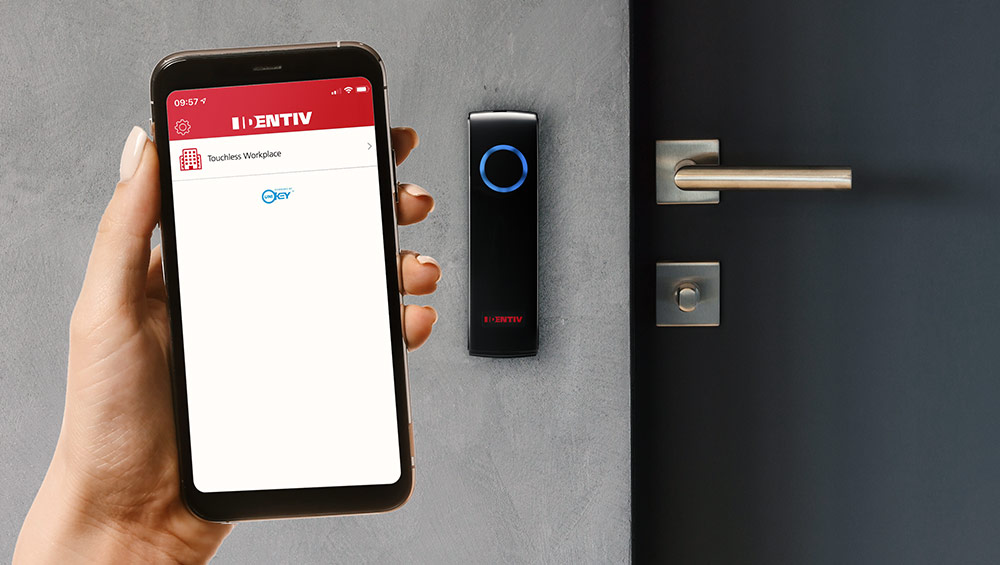
A
touchless access control solution limits physical contact with readers, allows for faster foot traffic, and provides higher levels of convenience for users. Biometrics can be one example of contactless solutions but other options include Bluetooth technology. Bluetooth allows for completely frictionless access and no touching is needed. For instance, you can enable your phone to be your physical credential with the simple addition of an application. When you need to enter your workplace, keep your mobile device in your pocket, wave your hand by the reader and the door unlocks.
In
some systems, no reader is even required at the door. These modern access control solutions are built on a software-defined architecture that uses the location of your mobile device to determine your proximity to a door for hands-free ingress and egress.
In addition,
smart card readers can be optimized with multiple frequency options and keyboard emulation. Ideal for employers who use various solutions for logical access, these types of high-frequency cards can work with most time and attendance systems. Employees simply need to tap their card to the reader to clock in.
Mobile Applications
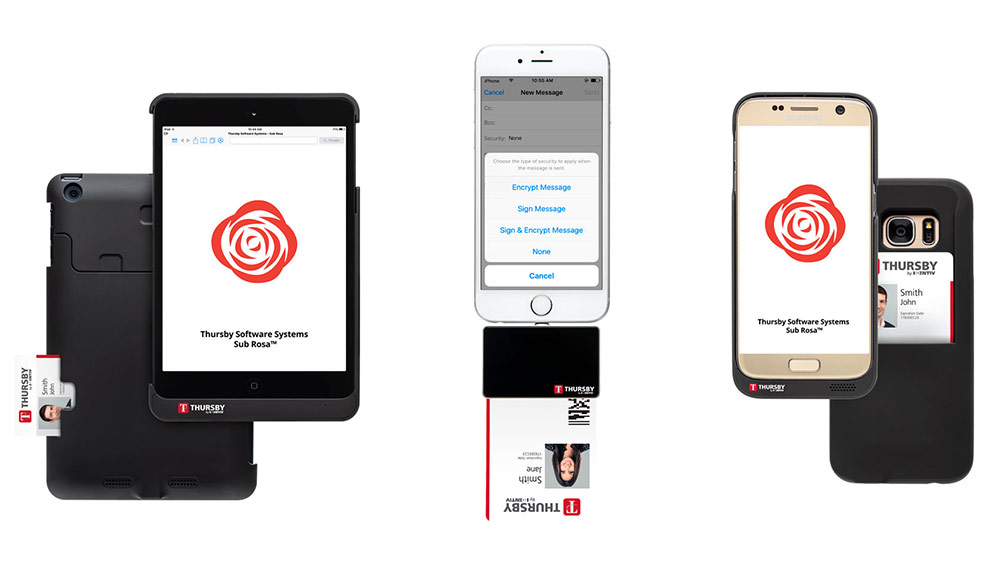 Mobile applications
Mobile applications are also hugely valuable in high-security environments to streamline cybersecurity efforts and make remote work more accessible. Advanced mobile applications designed for mission-critical environments provide users with the ability to edit and sign PDF documents from their iPhone, iPad, or Android phone or tablet, using their CAC, PIV, or derived credential. Additionally, users can access two-factor websites; sign, encrypt, and decrypt emails; and view, edit, and create calendar events. As some employees return to work, but others continue to work remotely, these types of solutions prove valuable in ensuring documentation and approvals are met.
Contact Tracing

If a person enters a building and is later symptomatic,
contact tracing can pull a report of everyone who entered through the same door. They can then be notified to either get tested or self-quarantine. This better positions the facility to be proactive in their response to a potential outbreak, while simultaneously providing employees with peace of mind that there are proactive measures in place to keep them safe. In many cases, this is a free feature that customers can request as they prepare for re-entry.
We live in a world where technology is easing once time-consuming and complex processes, and security is no different. As we move through this evolving situation, we hope our tips help and that you stay safe, smart, and secure during this time of transition. We’re all in this together and need to keep it that way.